What we secure. What you configure.
Platform security (FNTIO)
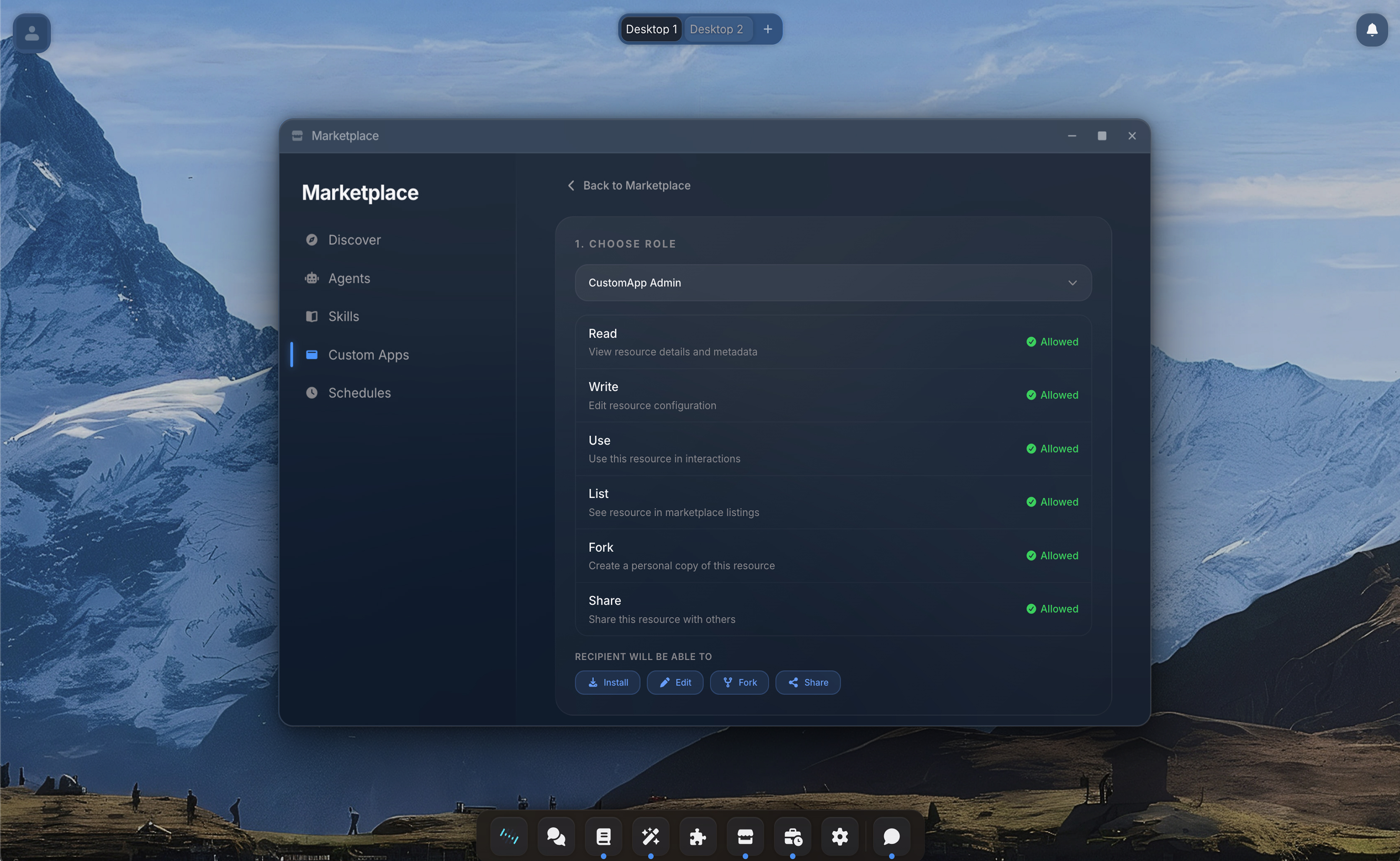
Tenant isolation, data encryption at rest and in transit, SSO, SCIM, RBAC, audit logging. The platform is secured with enterprise best practices.
Agent guardrails (FNTIO)
Sandboxed execution, credential injection invisible to agents, network proxy with domain allowlists, tool approval flows. These mechanisms are built into the platform and enforced automatically.
Agent scope (You)
Which connections an agent can use, which vaults it can read, which tools it can call, which domains it can reach. Every integration is a deliberate action by an admin or user. The platform provides the controls, your team defines the policy.
Agent behavior (Shared)
AI models are constantly improving and every organization has different trust levels. If an admin grants an agent permission to send emails via Outlook and the agent uses that capability in an unexpected way, that falls under the configured scope. We ensure the guardrails hold. Your team decides how wide the guardrails are.
Built for security teams.
Click to expand each section.